Protect data and devices
Everyone must take steps to secure all their devices and data to reduce the risk of a data breach.
Portable devices (such as smartphones and tablets) are mobile computers and are exposed to many of the same malware (such as viruses) as desktop computers.
Encrypting data makes the information unreadable unless the viewer uses a secret key to unlock it, called decryption. It can be applied to both stored data, computer drives or USB storage devices and data transferred through networks.
Always lock or log out of devices when leaving them unattended, even if it's just for a moment, and take any portable devices and sensitive notes with you. This will help prevent unauthorised access and ensure information is kept secure.
Prevention
To protect computers from infections:
- Don't click on links in suspicious emails or those from unknown sources.
- Don't download files or software from websites that aren't well known to you.
- Ensure your personal computer is running the most up to date version of antivirus.
- Always scan removable media (such as USB drives) before using it. If the USB is from an unknown source do not plug it into your device.
- Always save email attachments and scan for viruses before reading or opening.
- Always scan files downloaded from the internet.
UWE Bristol managed computers automatically scan for Malware and have up to date antivirus. However, if you are not sure, you can manually scan files for viruses with Sophos Endpoint antivirus. For guidance with your personal antivirus software, consult the manufacturer's website.
Infections
Signs a computer may be infected:
- problems connecting to networks
- computer freezing, suddenly slow to respond or crashing
- modified or missing files
- appearance of strange files, programs or desktop icons
- emails or messages sent automatically.
If you suspect a UWE Bristol computer is infected with a virus, contact the IT Service Desk immediately.
Any delay could lead to the loss of important data.
About Malware
Malware is short for malicious software, meaning it can be used to compromise computers (Windows, iOS, MacOS, Android and Linux), steal information, bypass access controls and can spread rapidly from one computer to another, causing disruption and damage.
Spyware is used to track user input, their activity and steal account passwords or sensitive information.
Ransomware attempts to encrypt personal documents and files, rendering them unreadable unless the victim pays the attacker money to decrypt them.
How to protect your data and devices
- Encrypt emails
- Encrypt Microsoft files
- Encrypt other files
- Encrypt iOS mobile devices
- Encrypt Android mobile devices
- Encrypt Microsoft mobile devices
- Encrypt a USB storage device
Encrypt emails
Emails are not secure as they can be read while they travel over the internet to the recipient.
Attach confidential information in an encrypted file or restrict access to an email by using the steps below:
- Create or open the email to be sent.
- Click Options > Permission.
- Select an option from the dropdown list:
- Encrypt-Only - This message is encrypted. Recipients can't remove encryption.
- Do Not Forward - Recipients can only view this email.
Email safety
- Always think before you click links, open attachments, or download files in emails you receive, regardless of who sent them. (More information on suspicious emails can be found via How to spot phishing.)
- Report any suspicious messages by using the Report Message button or by forwarding the email to spamtrap@uwe.ac.uk and deleting it from your inbox for the Information Security team to investigate.
- Don't respond to suspicious email messages from:
- anyone, including IT Services, that ask you to confirm your password or personal information or demand an immediate response or threaten loss of accounts or services.
- unrecognised senders.
- Carefully consider if sending confidential information by email is appropriate (for example, an alternative and more secure method is to send a link from a secure storage area).
- When sending confidential information by email, clearly state confidential in the subject line and protect the email by restricting access.
Remember, if an email is too good to be true, it probably is!
Encrypt Microsoft files
Add or remove a password to control access to a document. This will protect files and enable restricted or confidential information to be securely shared outside the UWE Bristol network.
- Create or open a document that needs password protecting.
- Click File > Info > Protect Document > Encrypt with Password:
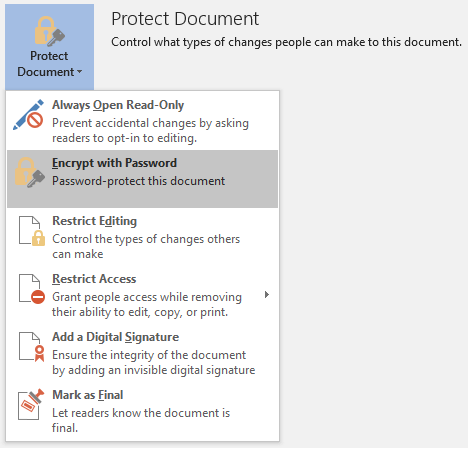
- Enter a strong and memorable password.
- When sharing the file (such as email) ensure you share the password using a different method (for instance, text, phone, planned protocol).
Please note: passwords cannot be recovered if lost or forgotten.
For further information on protecting and restricting Microsoft files, please see Microsoft support.
Use the latest version of Microsoft Office provided by the University because this provides the best protection.
Encrypt other files
7-Zip is the preferred file archive software at UWE Bristol. You can use 7-Zip to protect (encrypt) files that are not Microsoft (such as Word, Excel, PowerPoint).
Encrypt using 7-Zip
- Right click on the file / folder that you would like to encrypt, and select 7-Zip > Add to archive…:
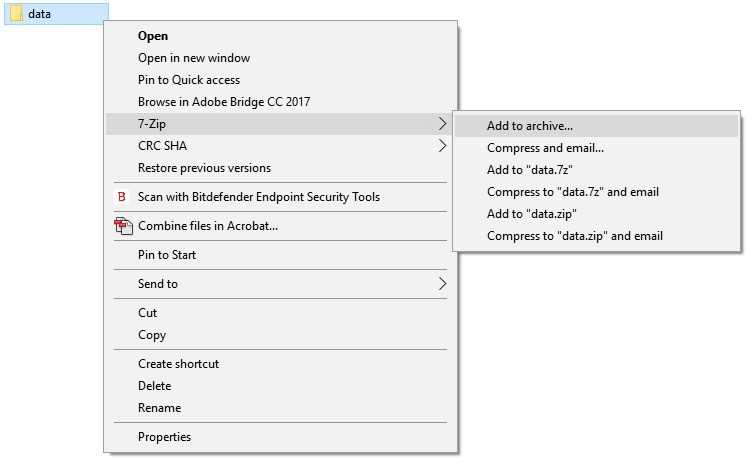
- In the 'Add to Archive' window, select the following:
- Archive: Enter the name you wish to give the file
- Archive format: zip
Please note: when encrypting a file using zip only the file content will be protected, the file name will still be visible. To protect the file name change the archive format to 7z. - Encryption method: AES-256
This method is more secure than ZipCrypto (the default). - Enter password and Reenter password: Enter a password.
This will be needed to open files. To ensure your data is properly protected, choose a strong password
- Click OK.
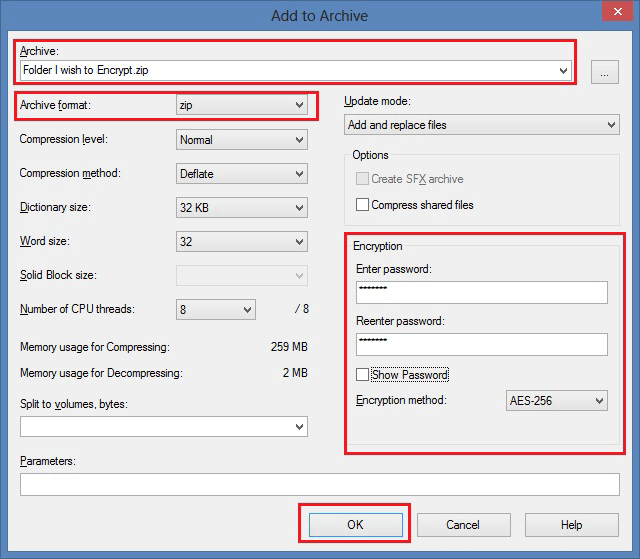
Remember to share the password using a different method to the way you share the file.
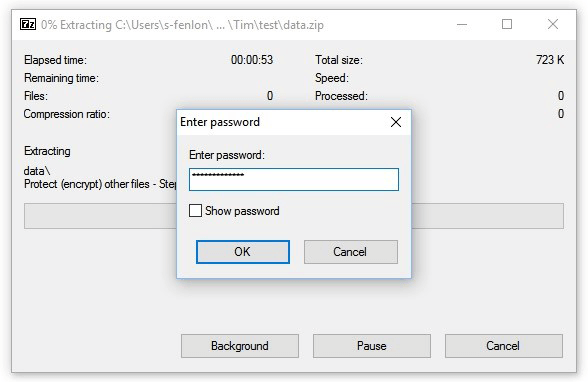
Open a 7-Zip file
- To open an encrypted archive file, right click and select 7-Zip > Extract Here or Open Archive:
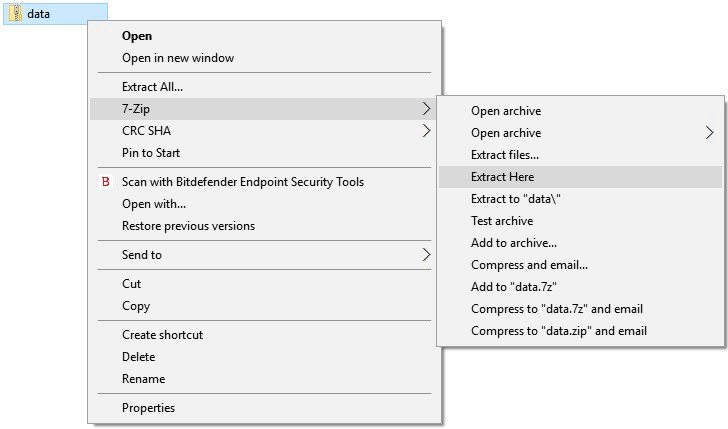
- Enter the password to open your files:
Encrypt iOS mobile devices
Protect your personal devices with antivirus software, turn on automatic software updates, update your web browsers and any other software.
If you store data, emails or photos on a personal or University-managed portable device (such as smartphone and tablets), then you should encrypt the device to protect this information.
When a passcode, Touch or Face ID is enabled on a device running iOS 8 and above, full encryption is turned on automatically.
To activate this, complete the following steps:
- Launch the Settings app on your iPhone or iPad.
- Select Touch ID & Passcode or Face ID & Passcode from the list of available options.
- Now simply tap Turn Passcode On and enter your passcode of choice.
A longer alphanumeric passcode is recommended but you can also use a six-digit PIN code.
Avoid four-digit PINs as your passcode. You can change this PIN length in the 'Passcode Options' within the 'Set Passcode' screen.
To confirm if encryption is enabled:
- Launch the Settings app on your iPhone or iPad.
- Select Touch ID & Passcode or Face ID & Passcode from the list of available options.
- Scroll to the bottom of the screen and you should see the sentence 'Data protection is enabled'.
Encrypt Android mobile devices
Protect your personal devices with antivirus software, turn on automatic software updates, update your web browsers and any other software.
If you store data, emails or photos on a personal or University-managed portable device (such as smartphone and tablets), then you should encrypt the device to protect this information.
- Go to your Android phone or tablet’s Settings.
- Select Security.
- Select Encrypt Phone.
- If you have not set a passcode, you will now be asked to. Follow the instructions and set a strong password when prompted.
- This will encrypt your device memory, but will not encrypt the contents of any SD card used in the phone. Take care not to store confidential or restricted data on removable storage unless it has been encrypted.
Encrypt Microsoft mobile devices
Protect your personal devices with antivirus software, turn on automatic software updates, update your web browsers and any other software.
If you store data, emails or photos on a personal or University-managed portable device (such as smartphone and tablets), then you should encrypt the device to protect this information.
- Go to your Windows Phone or tablet’s Settings.
- Select Device Encryption.
- Turn on the Encryption option.
- If you have not set a passcode, you will now be asked to. Follow the instructions and set a strong password when prompted.
- This will encrypt your device memory, but will not encrypt the contents of any SD card used in the phone. Take care not to store confidential or restricted data on removable storage unless it has been encrypted.
Encrypt a USB storage device
UWE Bristol's encryption solution is Microsoft's BitLocker.
To encrypt a USB storage device using BitLocker:
- Right click on the icon for the device in the My computer menu and select Turn on BitLocker…:

- You will be prompted for a password.
This password will be used to decrypt the device and will need to be used to access your files in the future. To ensure your data is properly protected, choose a strong password. - BitLocker will begin encrypting your USB device, which may take some time.
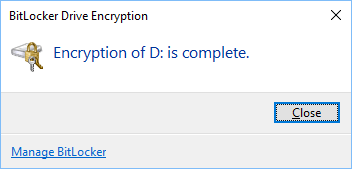
Do not remove the USB device before encryption is complete, otherwise the files on the device may become corrupted. - When the message below appears, the drive is now encrypted and safe to use:
- When the encrypted drive is inserted into a computer, it must be unlocked using the password before any data can be accessed:
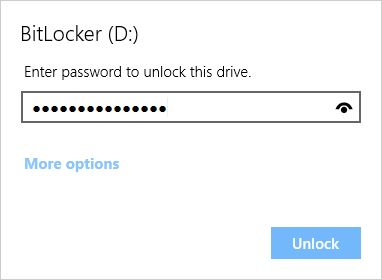
- Once the device has been successfully unlocked then data stored on it can be accessed as normal.
Updating devices
Restart or shut down your devices every day to keep them updated and protected. They’ll receive vital security and software updates that’ll help keep your information safe.
Shutting down will save a bit of energy, too. Good for the environment, good for you.
Mac computers are just as vulnerable to viruses and other threats as Windows PCs are, so please make sure you keep them updated.

You may also be interested in

Microsoft 365
Information on Microsoft 365 features and how to install them, including: email, Microsoft Office and OneDrive.

Passwords
Advice on strong passwords, keeping them secure and password managers.

Information Security Policies
All UWE Bristol users must read and abide by the information security policies and regulations.

Data protection
UWE Bristol's privacy information including GDPR statement, Data Protection Impact Assessments, and privacy notices for staff, students and alumni.
